THE RUNDOWN
Rocking headlines earlier this year, a Chinese-backed hacking group known as Volt Typhoon managed to breach a number of U.S. critical infrastructure facilities and position themselves for what could have been immensely destructive attacks.
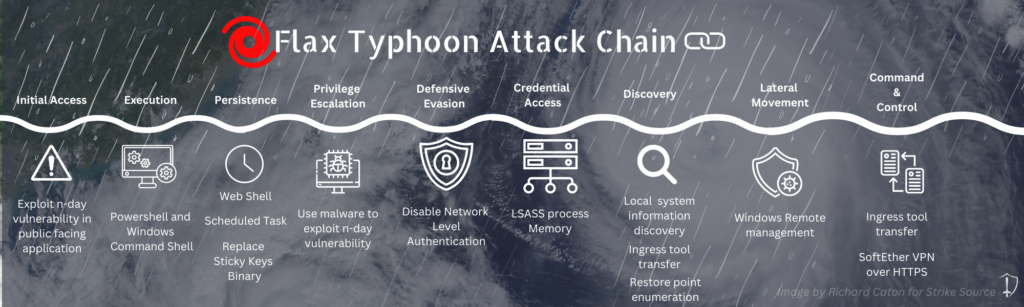
Now, another China-based group, Flax Typhoon, has been identified by Microsoft. Operating on a lower level of sophistication but effective in their own right, Flax Typhoon has been targeting unpatched edge devices such as VPN, web, and SQL applications. Emulating Volt’s tactics, techniques, and procedures (TTPs) by making use of living-off-the-land binaries (LOLBins), Flax evades detection. Their primary focus has been Taiwanese organizations, spanning the education, IT, government, and manufacturing sectors.
Attacks like these are occurring more frequently as China ramps up its cyber warfare capabilities; officials are concerned these discoveries are part of a preparation for a military invasion of Taiwan.
Volt Typhoon’s Motivations
The attacks span numerous sectors, including communications, government, manufacturing, utility, transportation, and more. Volt Typhoon targeted several areas in the U.S. but focused primarily on the island of Guam. Guam houses several military installations and plays a key role in U.S. strategy in the South Pacific.
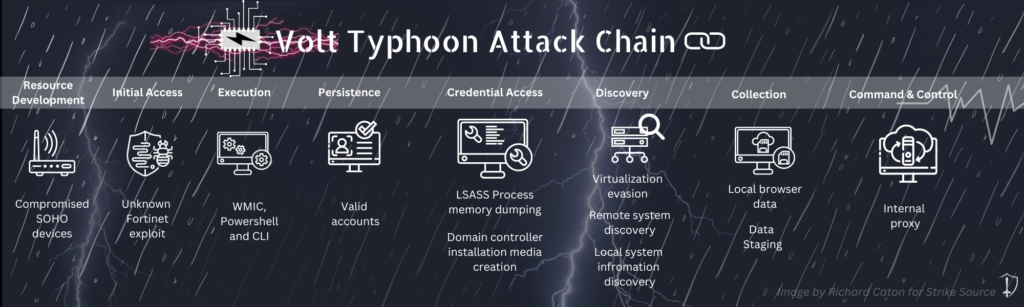
It is believed that Volt Typhoon gained initial access to systems through internet-facing FortiGuard devices and extracted credentials which they then used to access compromised systems. Once inside the target environment, Volt Typhoon used command line tools to discover information about the system and launch their attacks. Using network devices like home routers as proxies, Volt Typhoon was able to disguise the origin of their activities. This made it seem as if network traffic originated from a source geographically local to the compromised host. Experts say these recent attacks are concerning because Volt Typhoon appears to be shifting from data monitoring and extraction to positioning for “digital sabotage”. Microsoft’s recent blog post on the topic, stated “this Volt Typhoon campaign is pursuing development of capabilities that could disrupt critical communications infrastructure between the United States and Asia region during future crises.” Matt Olney, Director of Threat Intelligence at Cisco, stated that Cisco had responded to an incident at a critical infrastructure facility in which they suspected “sabotage preparation” as the primary goal.
Flax Typhoon’s Motivations
While the attacks employed by Flax Typhoon are simple to execute, they have proved highly effective in targeting low hanging fruit. Flax’s waves have crashed into overseas systems as well, with victims having been identified in South East Asia, North America, and Africa.
Flax’s objective appears to be espionage, however until this point, no evidence has proven them to be successful in achieving this goal. Despite this, it is important to remember that Volt Typhoon’s initial operations were focused on monitoring and data exfiltration, much like Flax, before making a shift to what could be seen as preparing to sabotage critical infrastructure.
A Love for LOLBins
The commonalities between the two end at their use of LOLBins to avoid detection. All the rage over this past year, LOLBins allow threat actors to subvert endpoint detection and response (EDR) tools and common antivirus programs by operating through common Windows utilities.
In order to obtain local administrator privilege, according to Microsoft, Flax Typhoon uses the open-source tools Juicy Potato and Bad Potato. Once their privileges have been escalated, Network Level Authentication is disabled for remote desktop protocol (RDP) and Flax modifies a registry key that specifies the location of sethc.exe. The modifications made cause the Windows Task Manager to be launched as a debugger for “sethc.exe”. Consequently, when one of their hackers uses the Sticky Keys shortcut on the Windows sign-in screen, Task Manager launches with local system privileges and a terminal can be opened to perform nearly any action.
The Bigger Picture
While the two groups may appear separate in their tactics and targeting, they are best understood when viewed through the lens of a bigger picture: China’s plan for reunification with Taiwan. China’s cyber warfare capabilities, which it continues to develop, are a core component of its overall military strategy.
While Flax Typhoon may aid in espionage against Taiwan, Volt Typhoon’s activities aim to disrupt any response by the United States in the event that China invades Taiwan. If China were to launch an invasion of Taiwan, they would have to account for foreign intervention, primarily from the United States.
Due to geographic distance, the United States faces a complex logistics situation if it were to send supplies or military aid to Taiwan in the event of an invasion. Military bases on Guam would play a key role in any response and are a major factor in U.S. military presence in the South Pacific, which China has been seeking to undermine. If they were able to disrupt critical infrastructure and communications on Guam through cyberattacks, it could severely delay aid to Taiwan, giving China the strategic edge needed for a successful invasion.
THE TAKEAWAY
The Volt Typhoon attacks on critical infrastructure in the U.S. extend beyond the usual cyber espionage campaigns. Experts are concerned that state-sponsored threat actors could use cyberattacks to sabotage or disrupt communications and other critical infrastructure, especially during times of crisis such as a conflict over Taiwan.
Flax Typhoon on the other hand, may be using their positions to feed intel to various Chinese departments, or as leverage for future attacks, much like the ones prepared for by Volt. It is of the utmost importance that we not only nip the low hanging fruit in the bud, but also continue to track these threat actors as they emerge around the world.
