THE RUNDOWN
Command-and-control (C2) servers are among the most valuable tools in a threat actor’s arsenal, enabling them to control tens of thousands of remote computers, from anywhere in the world. Entering cyberspace in the 90s, C2s have rapidly evolved over the past two and a half decades. What were once simple Internet Relay Chat (IRC) servers used to issue commands to a few hundred zombies have become a sophisticated weapon used by Advanced Persistent Threats (APTs) to facilitate espionage and destruction.
However, as they have evolved, they have also been made more readily available. Commercial C2s, used by red teams and penetration testers, have been cracked, listed, and sold on underground forums. These commercial hacking tools are marketed to legitimate users, and are made increasingly harder to detect, under the guise of emulating a real hacker on your network; in the hands of a cyber criminal, they pose a grave danger to organizations around the world.
An Introduction to C2s
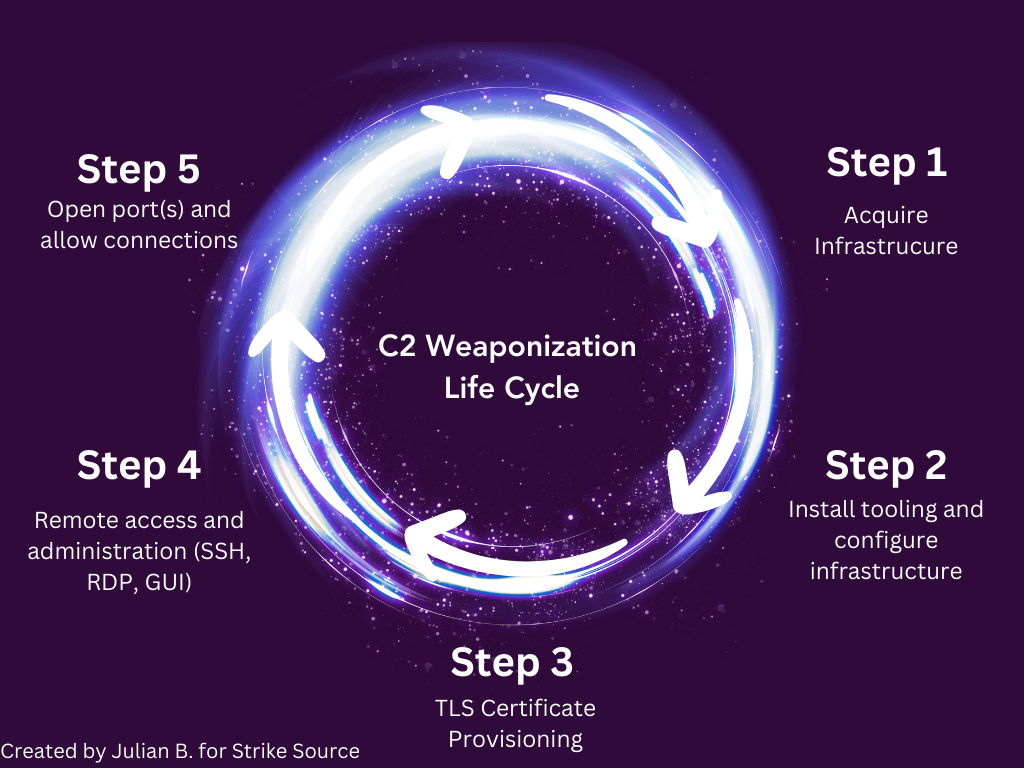
In its simplest form, a C2 is employed by hackers to maintain communications to infected machines, execute commands, exfiltrate data, and keep a hole through a network open for them to come and go as they please.
Early botnets were controlled by IRC channels; compromised endpoints would connect to the IRC server and await commands from their master on a specified channel. As their popularity rose, hackers realized they could abuse this form of C2 to hijack botnets. Listening for servers which had high amounts of traffic, botnet hijackers would join the servers, study the communications, and take over the bots for themselves.
While uncommon, instant-messaging (IM) platform oriented botnets were a thing as well. Using AOL, MSN, or ICQ, the botnet owners would send their commands over IM, however they were deemed too inefficient. Only one bot could connect at a time, as accounts had to be shared, so the overall botnet size was limited.
A third type, web-oriented botnets, became quite common as time went on. Infected endpoints would reach out to the internet, connecting to a web server, and retrieving their commands. Many modern day C2s use a similar technique. Traffic made to look like a normal user visiting a website is harder to identify when combing through logs.
Nowadays, C2s come in all shapes in sizes with varying levels of sophistication. Web-oriented bots have continued to be all the rage, and while IRCs have died out for the most part, platforms like Telegram have risen up, with C2s following suit and using it as a platform to send out commands.
Back Orifice
On August 1st, 1998, a group known as the Cult of the Dead Cow released Back Orifice at DEFCON 6. The intention of its author was to demonstrate the security flaws in Microsoft Windows Operating Systems. Hailed as one of the most famous RATs of its time, Back Orifice had prolific use by script kiddies because of its ease of installation and simple Graphical User Interface (GUI).
Back Orifice was an early example of a command-and-control architecture being used by hackers to maintain access to an infected computer and steal sensitive data.
Trin00
Waking up on an August morning in 1999, administrators of the Minnesota University network were shocked to find their systems were unresponsive. Running in to respond to the incident, they found themselves the victims of the world’s first Distributed Denial of Service (DDoS) attack. For two days, their systems were ravaged by what would later be identified as coming from the Trin00 botnet.
Trin00 would later be used to take down the Yahoo website, which in the early 2000s was actually popular. It was believed to consist of thousands of computers and was infamous for leaving a folder on victim machines named “cry_baby”, where the attacker could leave a message.
Storm Worm
Nine years following the release of Back Orifice, Storm Worm rose to prominence. It was one of the first examples of a Point-to-Point (P2P) communications botnet, instead of communicating with a centralized server, Storm Worm would pass along commands through infected machines.
It attracted attention as it targeted anti-virus companies who downloaded the worm to analyze. When frequent requests from the same IP address were detected, the botnet would receive a command to launch a DDoS attack against it. Interestingly, the Estonia cyberattack in 2007 seems to have been perpetrated by the Storm botnet.
Amid disagreements with Russia about the relocation of a Soviet-era statue, Estonia was rattled with DDoS attacks against their parliament, banking systems, newspapers, and broadcasting agencies. “Today security analysts widely believe that the attacks were condoned by the Kremlin, if not actively coordinated by its leaders.” Andy Greenberg, author of the WIRED Guide to Cyberwar 23 August 2019. Storm Worm may have been one of the first condoned and coordinated DDoS attacks by a Nation-State.
MayDay
Following the lead of Storm Worm, MayDay used a P2P architecture as well. Once a system was infected, the program would reach out to a web server and register itself in the server’s database. In return, the bots would receive a list of all the other infected systems and establish P2P communications with them.
Emotet
One of the most prominent and infamous malwares, Emotet made its debut first as a banking trojan. Allowing threat actors to gain a foothold inside of a victim’s machine, they’d exfiltrate their financial information and use it to steal untold numbers of dollars.
Emotet has continuously evolved since its 2014 debut, in 2017 its operators shifted from banking to using it as a loader. Loaders are used for initial access to systems, lightweight and efficient; they allow the operator to evade detection and download further tools. Infecting thousands of computers, Emotet’s operators profited by renting out access to the systems on an Infrastructure-as-a-Service (IaaS) model. One of the more popular renters of these systems was Ryuk, who used their access to drop ransomware across systems, demanding tens of thousands of dollars to unencrypt.
In January 2021, coordinated efforts by Europol and Eurojust led to the arrest of several of its operators and takedown of their C2 infrastructure. Gaining access, through undisclosed means, law enforcement was able to disable the systems and redirect C2 traffic to infrastructure they controlled.
Cobalt Strike
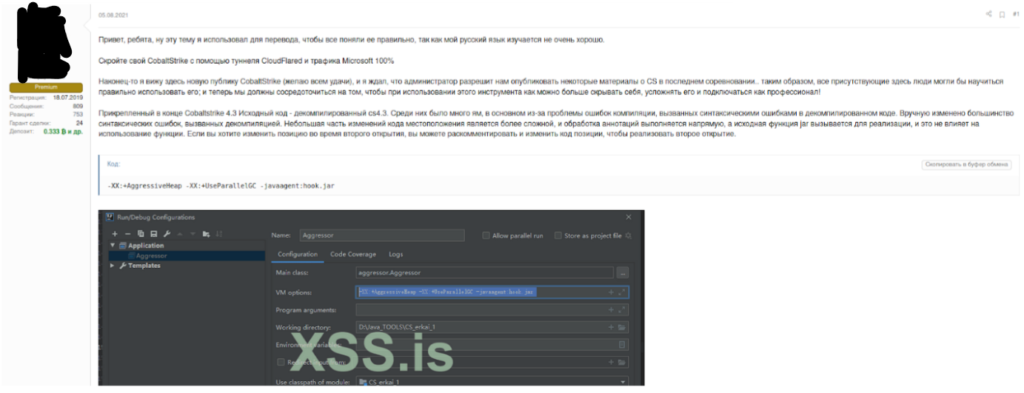
Cobalt Strike, an adversary emulation tool, commercially available to red teams and penetration testers has been an often commandeered weapon deployed by ransomware operators and APTs alike. Released in 2012 by Raphael Mudge, computer programmer and cappuccino maker extraordinaire, the tool’s slick design and evasive payloads have become infamous amongst network security defenders.
Using the typical client-server C2 architecture, Cobalt Strike provides two types of payloads Stager and Full Backdoor. These allow the operator to either “stage” their malware by sending a small malicious program, akin to Emotet, or Full Backdoor which runs in memory and connects back to the C2.
With a Cobalt Strike license, the operator gains access to their arsenal. Most notable of the kits available are the Mimikatz Kit, which allows them to dump credentials from memory, and Elevate Kit which allows them to integrate privilege escalation exploits. On criminal markets, Cobalt Strike modules are bought and sold to further the capabilities of threat actors.
Honorable mention goes to Chinese APT groups, one of the most prominent users of Cobalt Strike, according to Recorded Future’s 2022 Adversary Infrastructure Report, “The most commonly observed family on Shenzhen Tencent Computer Systems was Cobalt Strike, with 2,032 servers identified”. We will cover their OPSEC, or lack thereof, as it pertains to C2s in the subsequent article.
The Role of Markets
If you ever find yourself on an underground forum, clear or darkweb, one thing you’ll take quick notice of is the prevalence of cracked commercial C2 software.
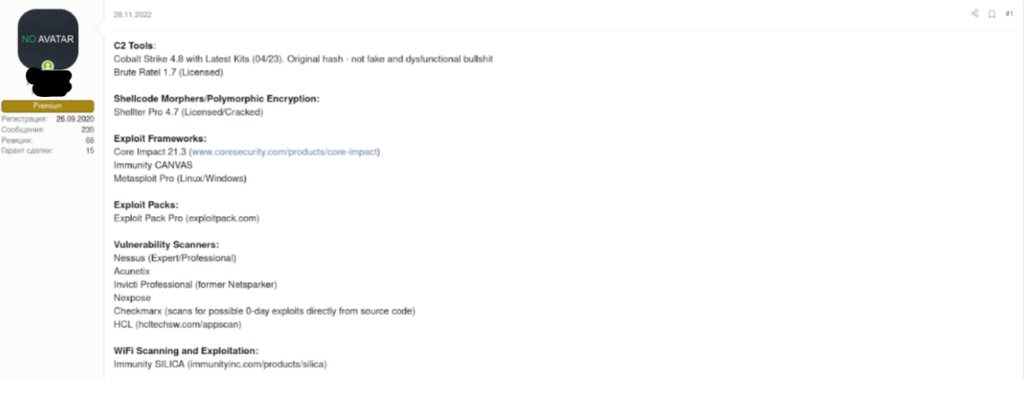
And while Cobalt Strike is the most prominent, it is not the only target of cracking and theft. Many of these tools are sold on markets for anywhere from $1,000 USD to $10,000 USD, paired with the latest custom exploits.
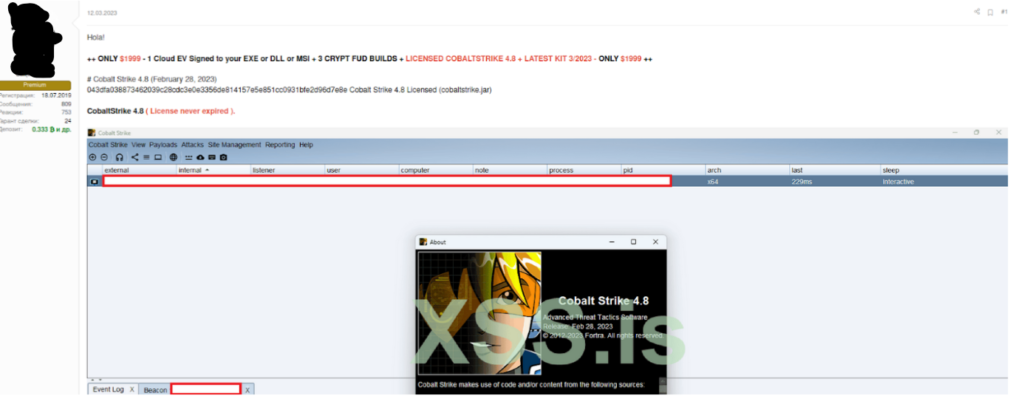
Not only do they provide the tools of the trade, the sellers offer comprehensive guides on how to hide it “like a pro!”. Perhaps Chinese APTs could learn a thing or two..
Markets serve as a means to proliferate the tools of the trade, monitoring these for trends can aid in identifying shifts in patterns, new tools, and exploits available to would-be attackers.
The Current State of Affairs
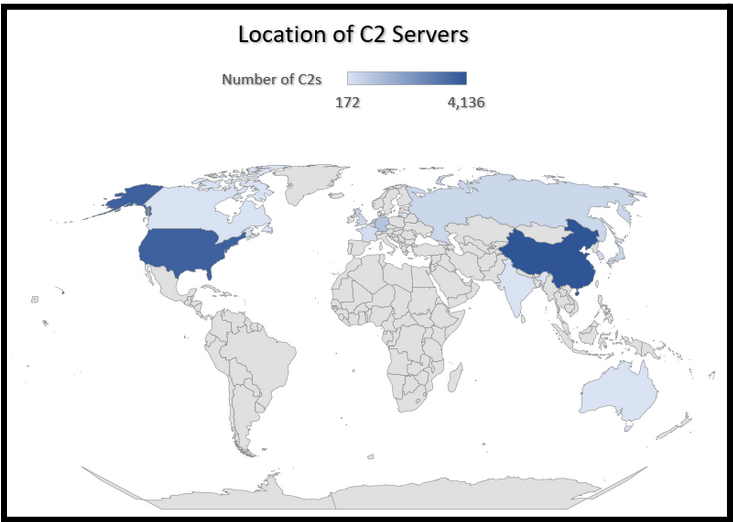
Using data obtained by Recorded Future, in their 2022 Adversary Infrastructure Report, Strike Source visualized the locations, by country, of C2 servers.
Leading the pack with over 4000 command-and-control servers, China dominates the landscape. Followed by the United States, coming in second, with nearly 3800. It’s important to note that this data does not identify which C2s are malicious, and which are not, and it may not be reflective of the true number of world-wide servers.
Dominating the landscape by a large margin, Cobalt Strike occupies 45% of the C2 market share in the wild. While many of the Cobalt instances may be legitimate, there is an unknown number being used for malicious purposes. The graph below illustrates a breakdown of the top five command-and-control servers identified by Recorded Future.
THE TAKEAWAY
Command-and-control servers are an ever-evolving tool utilized by red teamers and Nation States alike. As they increase in complexity and sophistication, defenders will continue to struggle to identify their activity on networks. Taking the temperature of the current landscape, both through monitoring illicit markets and forums, and mapping C2 infrastructure worldwide gives us a more thorough understanding of the current state of affairs. Using this data, defenders can better understand the ease of use, accessibility, and rampant threat that is posed by both commercially available and specially crafted C2s.
In this piece, we analyzed the C2s developed by commercial entities, and hacker groups. In our next article, we will delve into the world of Nation State command-and-control servers, their jaw dropping capabilities, and their OPSEC failures.
